Defense
Defense
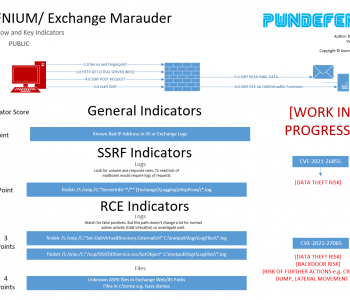
Thoughts on IOCs for Exchange Hafnium/ProxyLogon
Intro
This isn’t a rant, far from it but I’ve been working on this for over a week now and some major questions are sprining to mind with regard to how the IOCs and detection details released may have hindered response efforts. These vulnerabilities were known about since at least December 2020, there were months to get detection intel and scripts/tools ready for people (that’s if you don’t question why did it take so long). So I’ve put some of my thoughts down here on some of the challenges with the IoCs initially released and the detection tools etc. I’ll probably update this later but wanted to publish it before it becomes virtual dust! Read more “Thoughts on IOCs for Exchange Hafnium/ProxyLogon”