 Defense
Defense
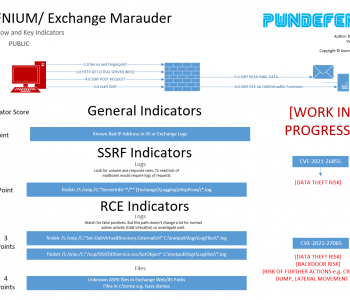
ProxyLogon (CVE-2021-26855) PoC and Metasploit Module Released
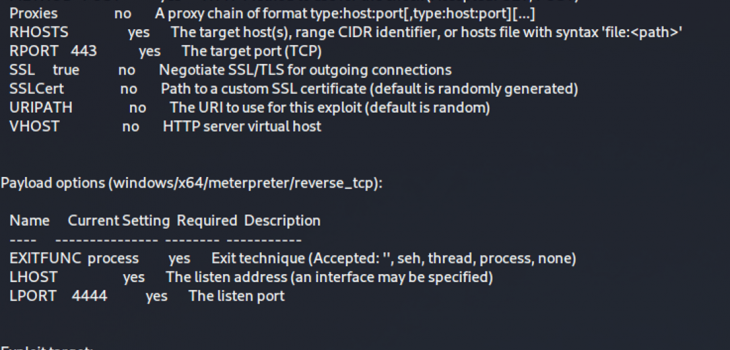
The last two weeks we’ve seen major activity around the world with defenders and criminals rushing to respond to the recent zero day vulnerability patches and then the race to reverse engineer the kill chain to create an explot. We saw a PoC fairly early but it required that you reverse engineer some exchange DLLs and/or TAP the 443 to 444 interface on an exchange server to work out how to weaponise it. Things however have progressed, 8 hours ago we saw a metasploit module go online:
Read more “ProxyLogon (CVE-2021-26855) PoC and Metasploit Module Released”