Defense
Defense
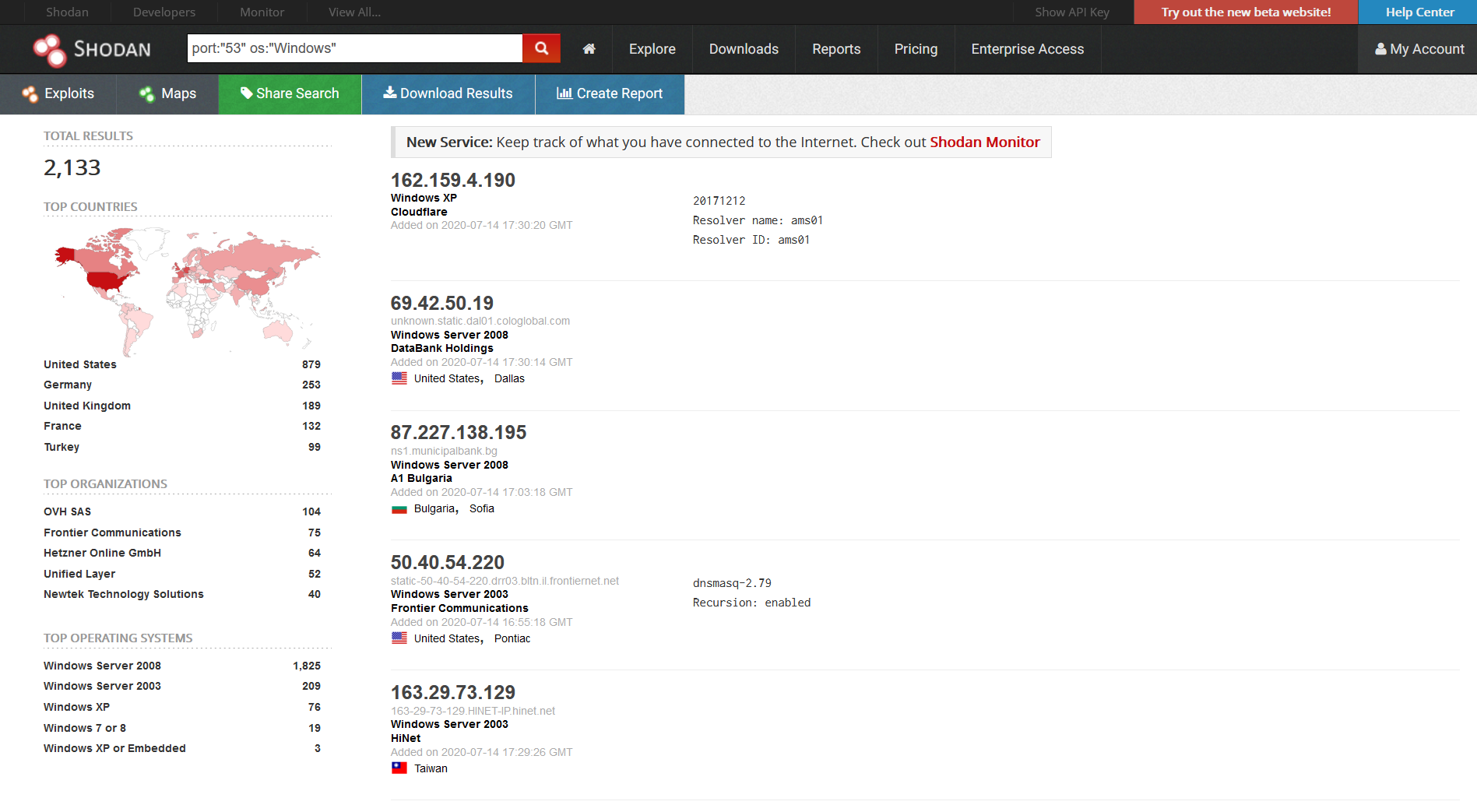
Secure Remote Access VPN
If your VPN can be brute forced, I hate to break it to you, but it’s got a bit of a design/implementation problem! Now I’m not going to go into VPN RCE’s (we’ve seen a lot of them in recent times) but let’s look at what we can do to protect our remote access services! Read more “Secure Remote Access VPN”