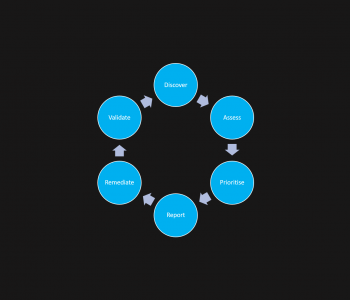
Defense
Defense
The anatomy of designing resilience, recoverability, and contingency into…
I want a simple way of restoring service in the event of a disaster
Foreward
I wrote this over 5 years ago and wanted to see if it stood the test of time – I also see too often that organisations don’t have the right capabilitites to recover so I figured this is a good post on the subject.