Hacking
Hacking
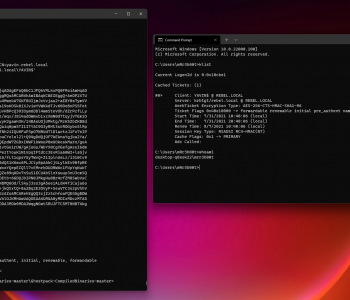
Active Directory Security Cheat Sheet
Ok you need to do some AD Security Auditing or Security Testing/Exploitation, great. Let’s look at some of the common misconfigurations and some tools to help you, a list of things will obviously not be the answer, you will need a method and process to go through from recon/enumeration through to exploitation and impact (effects), but that’s what google is for (and CTFs/Labs)! This post is just me jotting down some notes, hopefully they help defenders think about improving their posture.
Read more “Active Directory Security Cheat Sheet”