 Defense
Defense
Password Managers – The Good the Bad and the…
Good practise is not always good practise
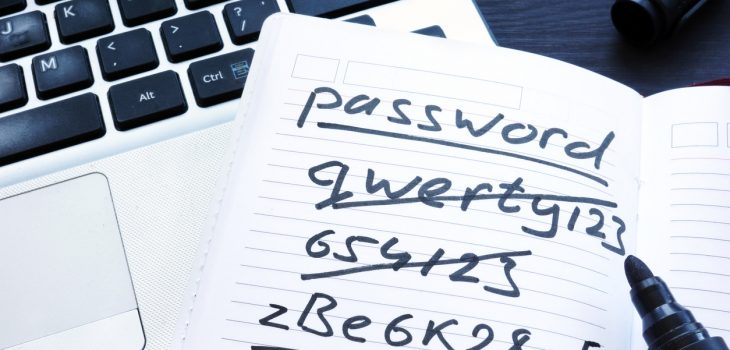
For years you might have heard to have a complex password you change regularly (like every 30 days to keep you safe from the hax0rs) but well… let us not lie, it is bloody terrible advice.
Password cracking, brute force attacks, credential stuffing and well mad human things like writing passwords down on post it notes under keyboards are hugely prevalent still. The other day I managed to see a password used on a corporate system which was “Thursday49”. Yep, I know I know we all know that a weak easily guessable, easily crack able password is not a good idea yet honestly, humans like things that work and are simple vs remember their 6 favourite books in reverse order with a complex character and capital letter. Read more “Password Managers – The Good the Bad and the Ugly”