 Defense
Defense
Good practise is not always good practise
For years you might have heard to have a complex password you change regularly (like every 30 days to keep you safe from the hax0rs) but well… let us not lie, it is bloody terrible advice.
Password cracking, brute force attacks, credential stuffing and well mad human things like writing passwords down on post it notes under keyboards are hugely prevalent still. The other day I managed to see a password used on a corporate system which was “Thursday49”. Yep, I know I know we all know that a weak easily guessable, easily crack able password is not a good idea yet honestly, humans like things that work and are simple vs remember their 6 favourite books in reverse order with a complex character and capital letter.
Real Problems, Real Attacks, Real Solutions
I once drew a diagram that showed a graduated way of looking at options, I cannot draw it again because I always draw the same stuff but let us look at things for a minute:
Really Bad
- Sharing passwords between accounts (we all are guilty of doing this at some point!)
- Using shared accounts
- Using generic accounts
- Using default passwords
- Using easy to guess passwords
Bad
Using password only authentication with internet connected systems
- Changing a password every x day
- Enforcing complexity e.g., Must include a capital, number, and a special character
- Not having protective controls e.g., account lockouts, monitoring etc.
- Writing passwords down in an insecure manner (e.g., on a post it notes, a book in a safe is not the worst thing depending upon your threat model and use case)
- Not Monitoring for breaches (e.g., Haveibeenpwned.com)
Not so good
- Using 2 Step Verification (it is better than just a password in some cases, but it is lame, do not do this)
- Using SMS for 2FA (Sim swap attacks are real)
Better
- Use random pass phrases or passwords for each account (ideally use a separate account name but let us get real for business’s that is not reasonable given most of the technology involved currently)
- Using multifactor authentication
Best
- Using certificate-based authentication (PKI)
- Using Hardware Token Validation (PKI)
- Use unique account names/emails (e.g., aliases)
- Use long strong random passwords
Moving from bad to good
Now enabling 2FA/MFA and doing all the things of good practises here by hand is a problem, it is not really feasible these days. I mean hell I reckon I have over 500 accounts so there is no way I can remember that volume, and well everyone really has too many to remember.
Enter password managers
So, to solve this problem some bright sparks came up with the encrypted post it notes – a password manager! These are databases that are strongly encrypted with a master key (and potentially MFA, token based auth etc).
There are a few types of these which include:
- Online/Cloud Based
- Offline
They also come into flavours of:
- Open-Source Software
- Closed Sourced/ Commercial
- Hybrid
Now you might think that is the end of it, it is not. There are also freemium and different grades of services.
Options everywhere
Now I am not going to go into every option, and we need to recognise this, when looking at options you need to:
- Select options based on your threat model and risk appetite
- Conduct due diligence (e.g., if you are using a cloud service conduct supplier and service-based assurance activities)
- Consider your residual risks (what happens if the cloud service goes offline or you cannot get online etc.)
- Look out for-vendor lock in or changes to terms and conditions
Common Providers
There are a range of providers, each has their own pro’s and cons as well as different terms and tiers etc. Now here comes some of the Ugly in the world of cloud-based password managers. Recently
- Lastpass
- Bitwarden
- 1Password
And then we have the most popular open-source offering! KeePass. Now I am not going to go into each and everyone. I use a combination of cloud services and keepass, so I like to use both. However, this blog is aimed at high level guidance, you need to do what is right for you. However, we need to talk about challenges with using freemium cloud services. Today LogMeIn announced changes to the Free version of Lastpass:
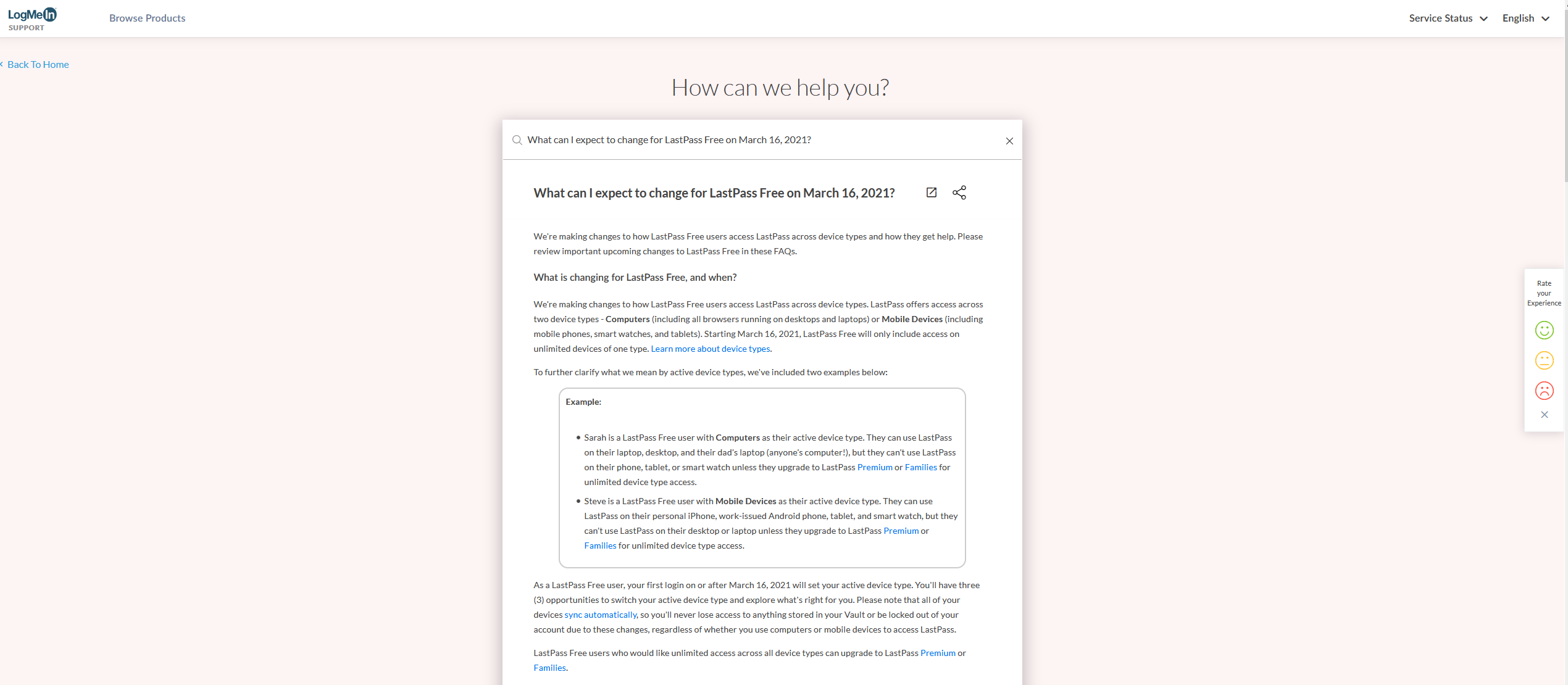
Now I do not want to go into everything here, it is their service and if they want to upset lots of its free tier user base, they are free to do so. But it is a grate point that we need to ensure that we are away of where our data is, how sensitive it is (passwords are crown jewels) and ensuring we have a plan for how we manage the lifecycle of these services. A simple way of doing this is to use FOSS and sync the data and keep backups etc. however that is not really a great model for the average consumer. Using a cloud-based password manager is probably the smart move, but as we have just seen with LastPass you get what you pay for and you are at the mercy of changes to terms and conditions (more likely if you use freemium style services).
Links
Summary
As with all technology usage both personally and from a business point of view, you need to consider:
- Constraints
- Resources
- Costs
- Architecture
- Supplier and Service Assurance
- Terms and Conditions
- Data Sovereignty
- Adoption, Training and Operations
- Ensuring there are risk assessments and backup plans
Sorry if you thought I was going to do the hard work for you, in the cyber security game you do not get the gains without the work, and I cannot pick your software for you. I can however at least show some options and considerations. Remember free is not normally free, and cheap is usually cheap so you often get what you pay for!
Be safe, be secure and may the force be with you!









