 Hacking
Hacking
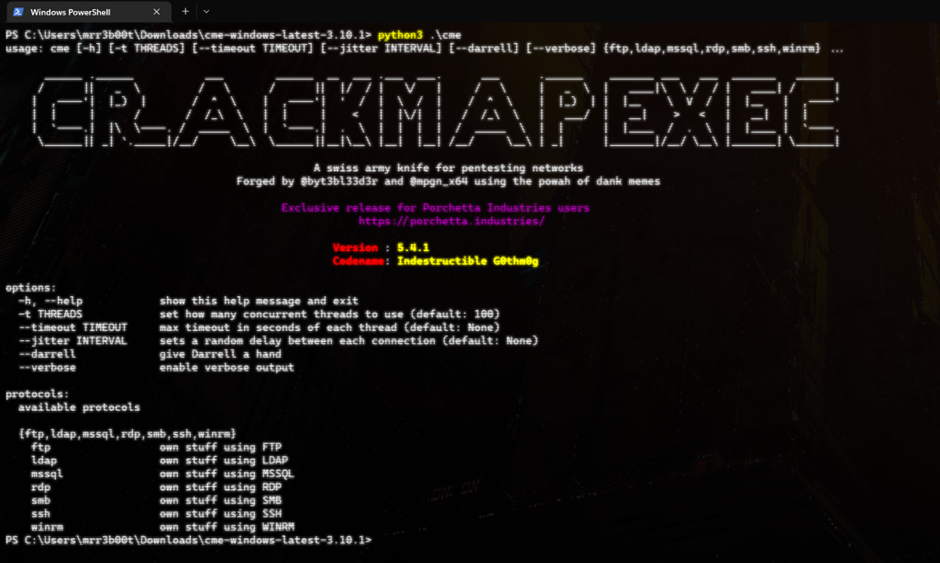
Ok this is going to be really short post, but expect more later! Did you ever want to run CME but you were stuck on a Windows machine? Well don’t worry you can! How do we do this?
First we download CME
Extract the zip file
Make sure you have python3 installed!
Install a dependancy!
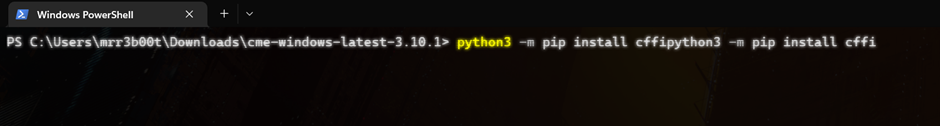
python3 -m pip install cffi
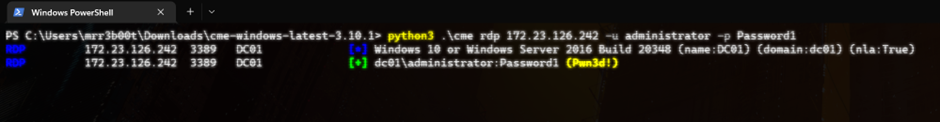
So now let’s attack something! (we will use creds that work on a demo vm)
| python3 .\cme rdp 172.23.126.242 -u administrator -p Password1 |
Success! We have pwn3d access to a server via RDP! (with NLA enabled)
The Official Instructions are here:
Installation for Windows – CrackMapExec ~ CME WIKI (porchetta.industries)
https://github.com/Porchetta-Industries/CrackMapExec
Detection
We are likely going to see both failure and success logs in the Security event log:
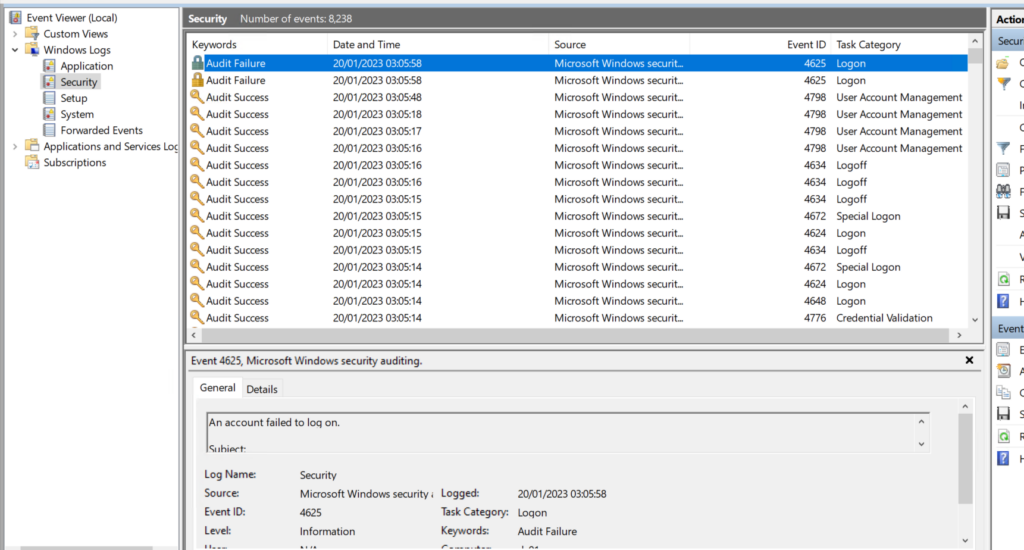
Event ID 4625 – An Account failed to logon – AUDIT FAULURE
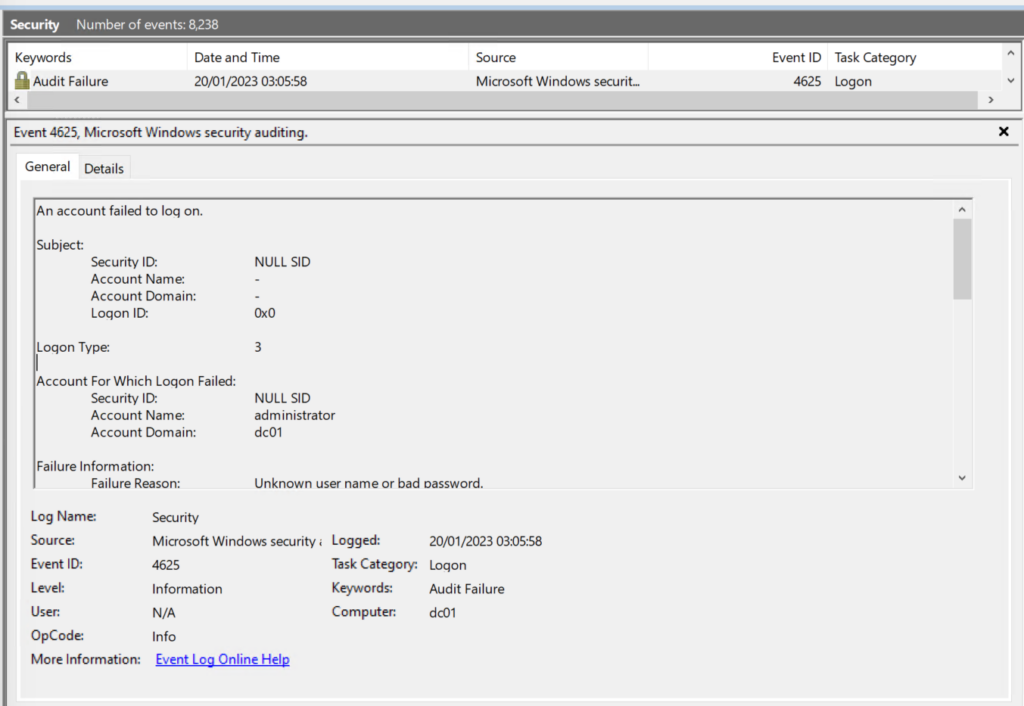
Here’s the data we see from this event:
| An account failed to log on. Subject: Security ID: NULL SID Account Name: – Account Domain: – Logon ID: 0x0 Logon Type: 3 Account For Which Logon Failed: Security ID: NULL SID Account Name: administrator Account Domain: dc01 Failure Information: Failure Reason: Unknown user name or bad password. Status: 0xC000006D Sub Status: 0xC000006A Process Information: Caller Process ID: 0x0 Caller Process Name: – Network Information: Workstation Name: – Source Network Address: 172.23.112.1 Source Port: 0 Detailed Authentication Information: Logon Process: NtLmSsp Authentication Package: NTLM Transited Services: – Package Name (NTLM only): – Key Length: 0 This event is generated when a logon request fails. It is generated on the computer where access was attempted. The Subject fields indicate the account on the local system which requested the logon. This is most commonly a service such as the Server service, or a local process such as Winlogon.exe or Services.exe. The Logon Type field indicates the kind of logon that was requested. The most common types are 2 (interactive) and 3 (network). The Process Information fields indicate which account and process on the system requested the logon. The Network Information fields indicate where a remote logon request originated. Workstation name is not always available and may be left blank in some cases. The authentication information fields provide detailed information about this specific logon request. – Transited services indicate which intermediate services have participated in this logon request. – Package name indicates which sub-protocol was used among the NTLM protocols. – Key length indicates the length of the generated session key. This will be 0 if no session key was requested. |
Event ID 4624 would be a success.
Defences
- Security Monitoring
- Account Lockout Policies
- and on MODERN Windows Devices you can configure account lockouts for SID500 (The builtin local administrator account)
- You can also have a second local administrator (maybe deployed with LAPS) and disable the local administrator account
- You may also want to CANARY Alert on .\administrator failure attempts etc.
- You may use windows firewall to set Authorisation on the connections
- You may use IPSEC
- You may use allow listing
- You might simply disable RDP
- You might want to use an RDGateway/RDweb service.
- Consider using Honeypots and Decoys
There’s ton’s of way to protect, detect and respond to defence!
Hope this helps people think about RDP authentication attacks and defences! It’s still used by criminals all both externally and on internal networks!







