 Education
Education
Introduction
There are tons of “products” for security awarenss training, however you might find that sitting and watching canned CBT videos isn’t your organisations thing or perhaps you want to see what other options there are available. Well for starts the UK NCSC has some free online security awarenss training (see further down the post), or you may want to actually spend time with your staff to make the learning a collaboarive experiance that drives engagement and communication. If the last one if your desired approach there are lots of ways to do this. One of which can be supported by a question based assessment, other ways include tabletop scenarios and incident simulations (i honestly would go with a blended appraoch if it was me!).
So to help people get thinking about this I’ve put together some example questions to drive the message about incident reporting, collaboration and education vs blame. So here we go, here’s some ideas for communication and some questions to get staff thinking about cyber security, sure they aren’t rocket science, but then it doesn’t need to be!
Example Communications
Security is everyone’s reasonability, that doesn’t mean everyone works in the Security Operations Center, but it does mean that people should act in a manner which is risk aware and considers negative business impact based on one’s personal actions.
We believe that we a strong security posture is enabled by:
- Education
- Communication
- Working together as a team
We also believe that when it comes to security events that following an incident, we should not seek to blame but to enhance our knowledge, understanding and future security posture.
Principle
In alignment with the UK NCSC CAF, our training of staff is alignment with:
“Staff have appropriate awareness, knowledge and skills to carry out their organisational roles effectively in relation to the security of network and information systems supporting the operation of essential functions.”
Questions
If an email looks suspicious, what should you do?
- Report it to IT/Security
- Open it
- Open it and click any links and submit credentials
If you believe you have been the victim of a phishing attack, what should you do?
- Report it to IT/Security
- Ignore it
You are emailed from apparently the CEO of a supplier chasing an overdue invoice, the email is out of character and is asking for payment to a specific bank account in the email. What should you do?
- Follow company policy and escalate the event to the finance department leadership and report to the security team
- Send the money immediately
You believe you credentials have been compromised, what do you do?
- Ignore it
- Contact the IT/Security team immediately
You need to grant access to a colleague to your mailbox whilst you are on holiday, which do you do?
- Delegate access via outlook
- Share your password with your colleague
It’s Monday morning, you are the first into the Office, when you log into your computer you see the following:
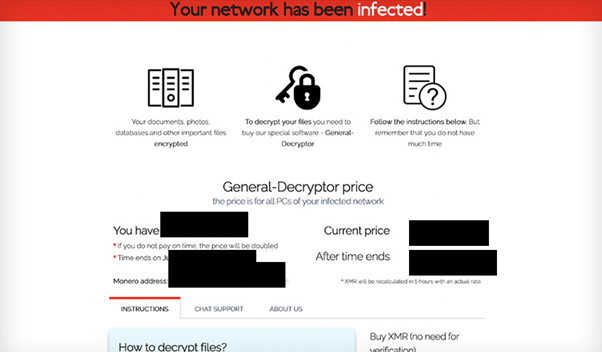
What do you do? (Choose two (2))
- Report the incident to the IT/Security team immediately
- Turn the PC off
- Disconnect the network cable or wireless device
- Ignore it
You notice the back door to the office is unlocked, what do you do?
- Ignore it
- Report it to the security team
You open an email, and you suspect it’s a phishing email, what do you do?
- Rick clicks the email, highlight SECURITY OPTIONS and Click Phishing
- Delete the email
- Ignore it
- Report it to the IT/security team
You notice a colleague acting suspiciously, what do you do?
- Report it to the security team
- Ignore it
You need to ensure your password is strong to reduce the likelihood of account credential compromise, which of the following is best?
- 8 characters with uppercase, lowercase, numbers, and a symbol, changed every 30 days
- Three random words (a passphrase)
To reduce the likelihood and impact of account compromise which should you use?
- Multi Factor Authentication
- An easy to guess password
Which of the following describes good practise computer account usage?
- Users do not have local administrator rights on their daily usage accounts which access email and the internet
- Local device administrator rights are provided to all staff
NCSC Free Security Training
https://www.ncsc.gov.uk/training/top-tips-for-staff-scorm-v3/scormcontent/index.html#/
Summary
So you could take the questions and use them with staff and keep tracking via a spreadsheet or whatever to demonstrate you traing staff.. that is one approach and it would probably pass an audit of sorts.
Education via CBT is great for some scenarios, but let’s be honest, forcing everyone to watch a set of canned videos, conducting an internal phishing assessment and blaming “the users” really isn’t the way to improve security culture in an organisation. That’s achieved through engagement.
In the end we can all get phished, we can all make mistakes, it’s far better to work with people, sure we should remind people of the foundations, and how/when to report incidents, but also we need to be practising with table tops and doing real life drills, this means with more than just the IT/Security team as well. Real life incidents need support from all the organisation. I’ve previously put together some examples of incidents to help people think about these as well:
Use what works for your organisation and it’s people, investing in being prepared with most things in life get’s a good return! oh and don’t forget there’s the NCSC excercise in a box: https://www.ncsc.gov.uk/information/exercise-in-a-box
There’s gold mines of useful tools in the world, lots of them just require some time!








