 Guides
Guides
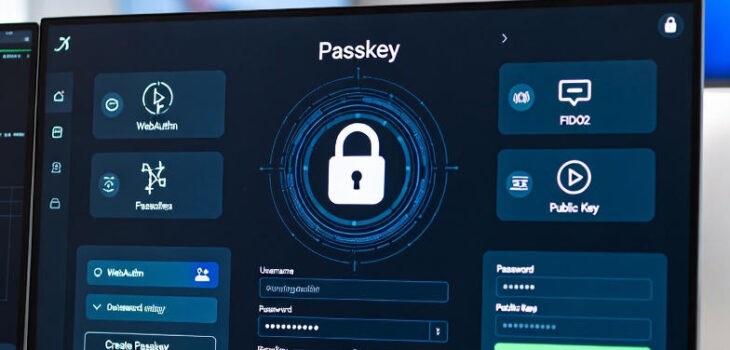
What are passkeys and how do they work?
Phishing, Brute Force, Data Breaches, Info stealers etc. are all ways in which people steal credentials. We’ve had this problem for decades, stealing something or guessing something people know is relatively trivial over the internet. This leads to a huge volume of the breaches we have seen over the last 20+ years. Whilst people seem to understand this, they don’t seem to know how to change to fix this…. (it’s not that we don’t know it’s that change is hard for lots of reasons). So there might be a solution with the adoption of passkeys! So what are passkeys?
Read more “What are passkeys and how do they work?”





