 Vulnerabilities
Vulnerabilities
Fast publish: If the past gives us any indication for the future, if you are running MoveIT you want to be aware of:
CVE-2026-4670 (CVSS 9.8 — Critical) is the dangerous one. Authentication bypass by primary weakness (CWE-305) — no credentials, no user interaction, network-accessible, with full CIA impact. CISA have tagged it “Automatable / Total Technical Impact”, meaning mass exploitation tooling is a realistic near-term threat. The absence of a public PoC today doesn’t give much runway given the MOVEit ecosystem’s attacker interest post-Cl0p 2023. – from Claude
CVE-2026-5174 (CVSS 7.7 — High) is the chained step. Improper input validation allowing privilege escalation within MOVEit Automation — low-privilege attacker, scope change, high availability impact. The natural kill chain is 4670 → unauthenticated foothold → 5174 → elevated access within the product → lateral movement. – from Claude
In the past there’s been a very short windows between patches and mass exploitation so I guess.. happy bank holiday weekend everyone!
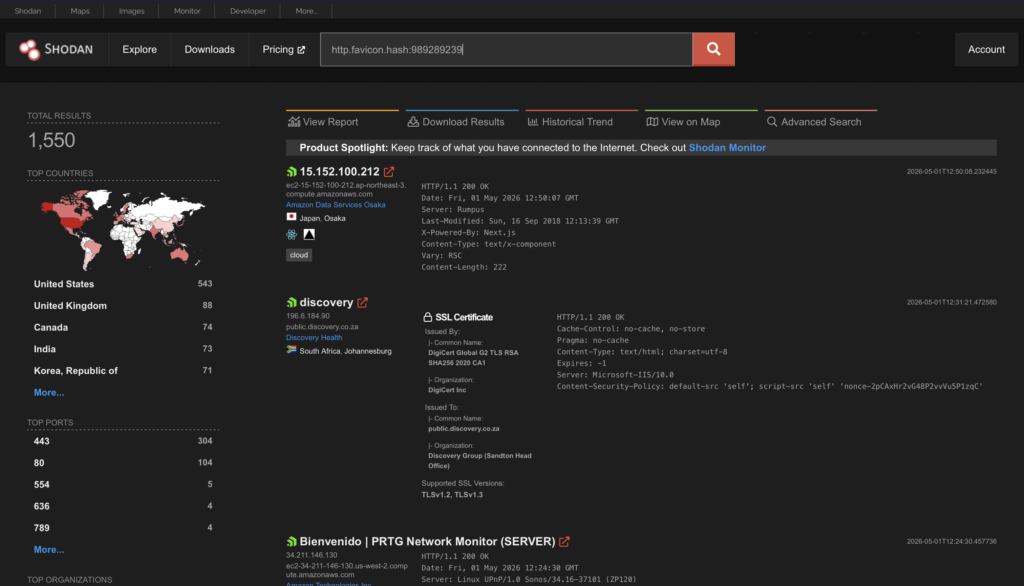
If you want to see the internet exposure on Shodan check out: https://www.shodan.io/search?query=http.favicon.hash%3A989289239
I guess we might be in for some cyber fun this weekend!








