17 Remote Code Execution Vulnerabilities in this month’s patch…
Windows DNS Server
This is really a major issues for Active Directory Domain Controllers.
CVE-2020-1350 : https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2020-1350
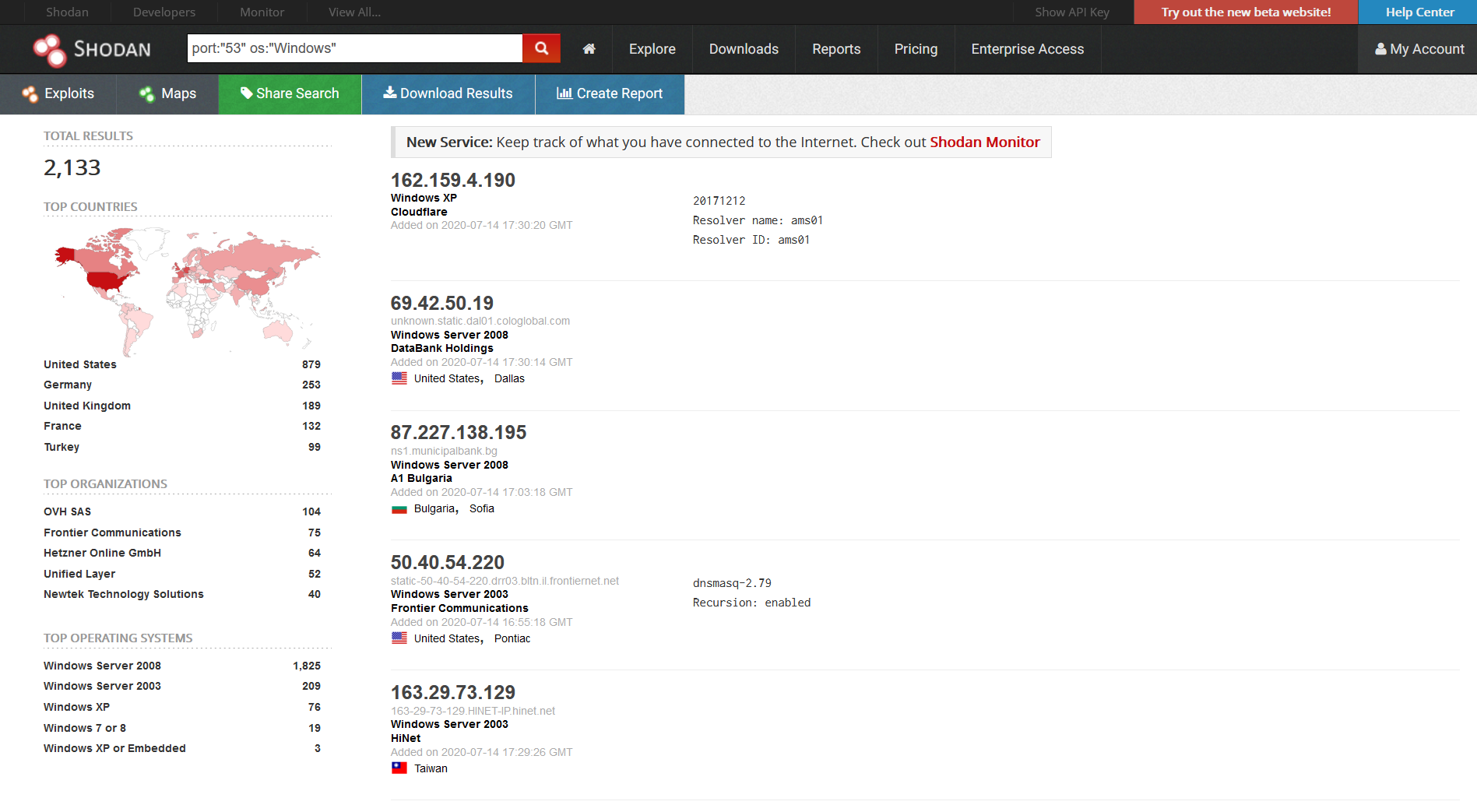
We can see there are 2,133 servers on Shodan that are exposed however this exploit doesn’t rely on exposure, a client request from inside the network to a malicious DNS server could be used to exploit the domain controller. Read more “17 Remote Code Execution Vulnerabilities in this month’s patch Tuesday release!”