AI
AI
one step closer to Skynet?
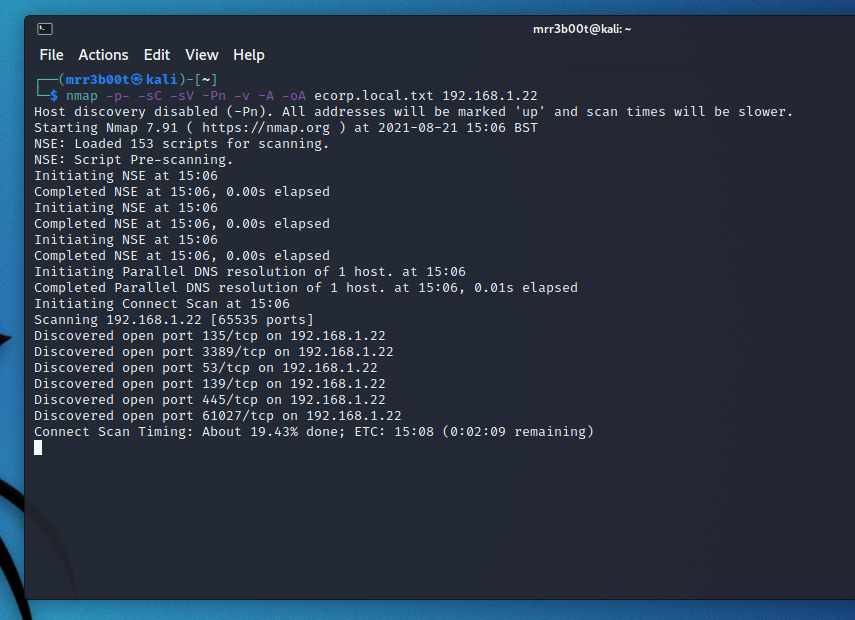
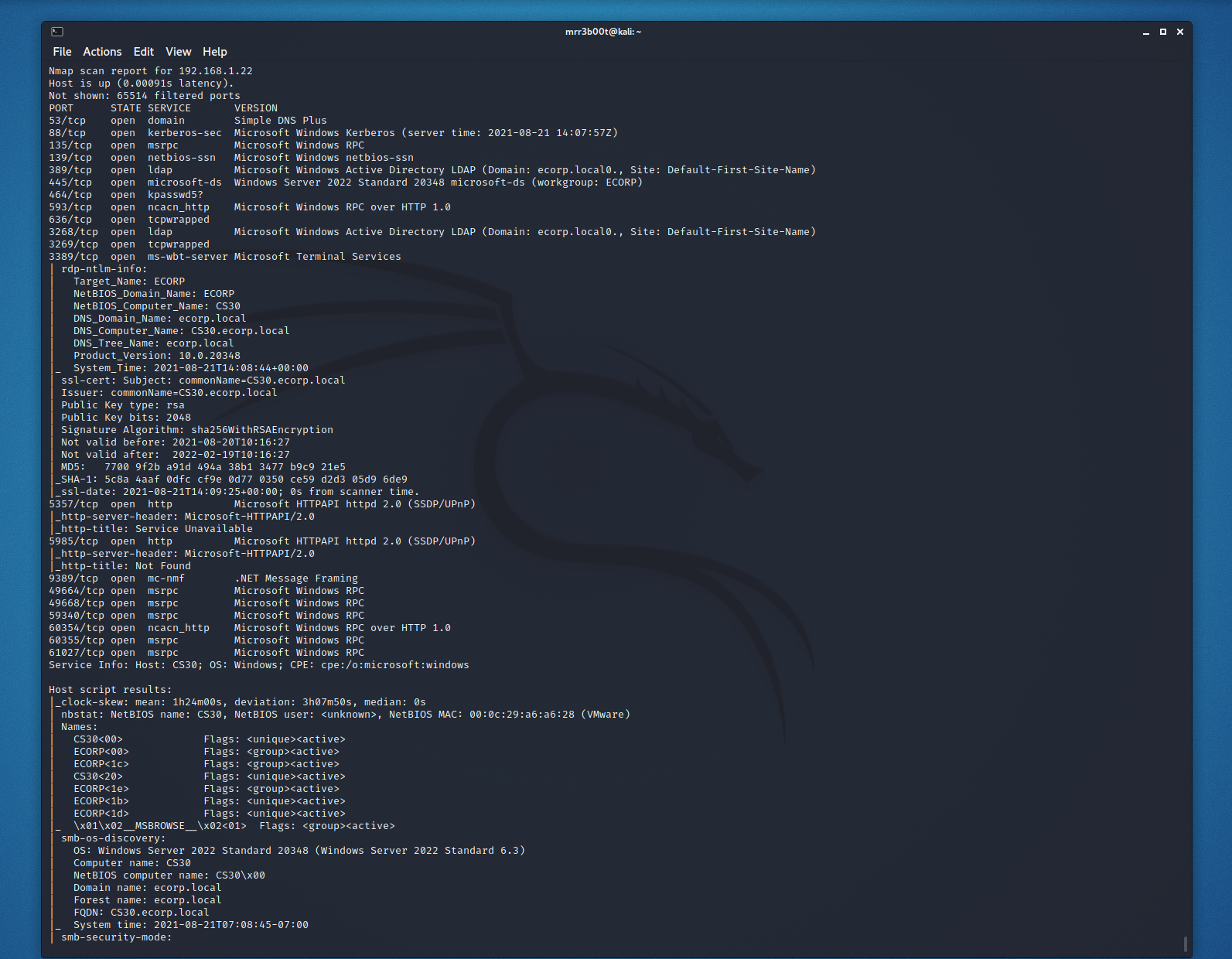
Yesterday I ran a pentest against an RDP server, the process was ok but not amazing, I had to provide more help than I would have liked, resource consumption and the idea it should keep going…. wasn’t great. The process and output wasn’t terrible at all but it didn’t blow me away.
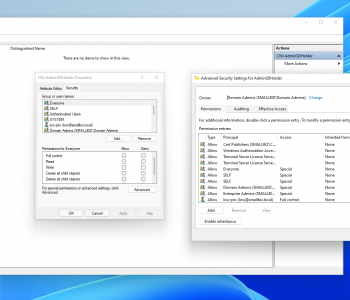
So today I wanted to see if Claude could take on as simple active directory lab! Now let’s be clear, there were I think one or two updates to the Claude client in that time! The Claude UI even changed look and feel! So I span up an AD lab I had made a while ago and got to work!