Education
Education
Why a SOC Without Triage, Analysis, and Remediation Is…
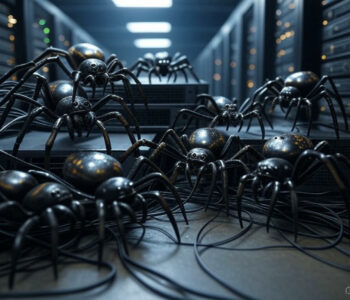
In the world of cybersecurity, the term Security Operations Center (SOC) carries significant weight. It evokes images of highly skilled analysts working around the clock to detect, respond to, and mitigate cyber threats. However, not all SOCs live up to this expectation. If a SOC lacks core functions like triage, analysis, assessment, and remedial action, it’s not truly a SOC—it’s merely a contact center masquerading as one. Let’s explore why these functions are non-negotiable for a SOC and why their absence undermines the entire purpose of cybersecurity operations.
Read more “Why a SOC Without Triage, Analysis, and Remediation Is Just a Contact Center”