 Defense
Defense
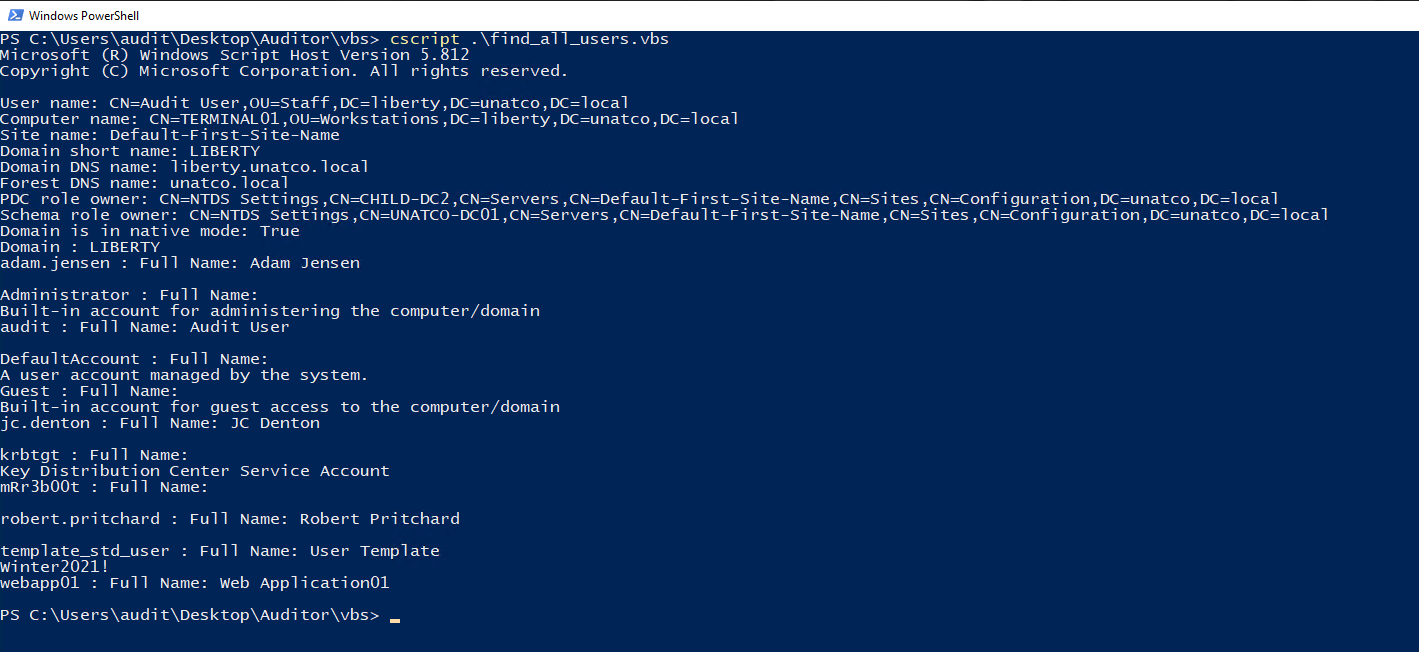
By default, a ‘domain user’ can read mostly everything in active directory. I’m not sure every sysadmin knows this as I often find passwords stored in the description filed (see the example screenshot, this was from a domain user with no third-party tools leveraged).
What this should show you is that things are not always as they seem, out of the box and with general system administration it’s easy to leave your organisations exposed to risks so let’s start the new year by getting our AD fit and healthy from a security point of view!
Things you can do to secure your domain
Ok let’s be clear – this isn’t THE LIST. There is a lot you need to do to secure your domain controllers, DNS, DHCP, workstations, members servers, the network, egress, ingress etc. So this is just some things that you can consider and look at implementing (without breaking the bank), it’s not everything! Now that’s over with let’s check out things we can do:
- Restrict users from adding machines to the domain
- Reset the KRBTGT account password (twice) every 90 days (required to reduce the impact of golden ticket attacks, there’s a script from MS to do this)
- Enable advanced audit configuration for event logging
- Deploy sysmon (consider looking at the SWIFT on Security or DODGE’s sysmon config)
- Audit and remove non required high privilege access groups
- Enforce account lockouts
- Set the confidentiality bit where apropriate (https://medium.com/beyond-the-helpdesk/easily-configure-confidential-attributes-in-active-directory-769bd2b9d12c)
- Check service accounts have a strong configuration (strong password (37+ chars) etc.) (see password rational below)
- Mark sensitive accounts to be prohibited from delegation
- Review accounts to ensure “does not require pre-authentication” is only enabled where absolutely required and that accounts marked with this have strong passwords (37+ chars) – I got asked by a friend why 37+ so here’s the more detailed version. I used this value as an arbritary make it really long so that no current realistic cracking scenario can work. I believe also that you want to ensure its of significant length to ensure the LM hash isn’t used.
There’s a ton of other areas to consider but here’s a quick boost to your new years Active Directory Domain system immunity! But like real life resolutions, it’s a marathon not a sprint!









