 Guides
Guides
Ever wanted to run honeypots all over the world but don’t want to deploy actual servers, or psudo servers everywhere? Ever wanted to run a C2 server but don’t want to expose your own IP and want a pool of redirectors? Well here’s a quick look at using SOCAT to forward HTTPS traffic from a VPS to a backend web server.
Process
Create a linux virtual machine in a cloud services provider:
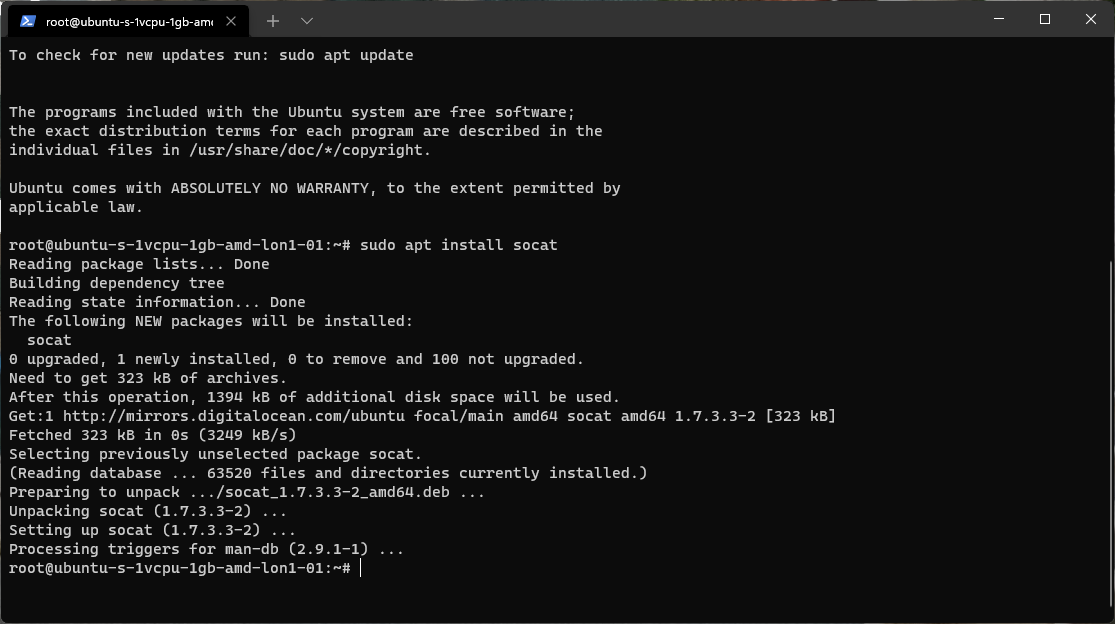
Install SOCAT
| sudo apt install socat -y |
Forward Traffic
| socat TCP4-LISTEN:443,fork TCP4:xx.xx.xx.xx:443 |
Bear in mind this is running as a user context. You will make this a “service” for production use.
Target Server
On the target server we will need to have a public IP or a NAT’d Public IP with the appropriate ports, in this instance TCP 443.
Firewalls
Now you will likely want to do this at the network fabric layer but for this instance we are going to use the host based firewall (we could use Iptables but for this UFW is nice and simple).
Install UFW
Apply a rule to allow inbound on TCP 443 from your redirector IP:
| sudo ufw allow from xxx.xxx.xxx.xxx to any port 443 |
Ensure UFW is enabled
| sudo ufw enable |
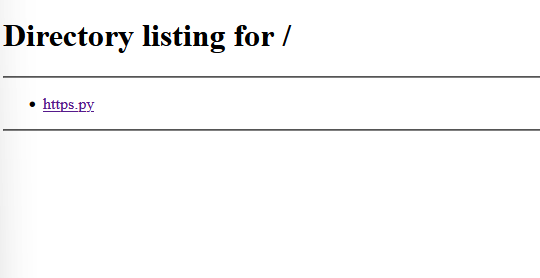
We will need an HTTPS service so for this demo we are going to use a simple python https server:
| https.py |
| #!/usr/bin/env python3
import http.server import ssl httpd = http.server.HTTPServer((‘0.0.0.0′, 443), http.server.SimpleHTTPRequestHandler) httpd.socket = ssl.wrap_socket (httpd.socket, certfile=’../server.pem’, server_side=True) httpd.serve_forever() |
We will need a certificate, for this demo we create a self-signed cert:
| openssl req -new -x509 -keyout server.pem -out server.pem -days 365 -nodes |
You will want to keep the certificate out of the web server path (hence the ..\) so make a subfolder named server. Clearly this isn’t amazing as a web server etc. but this is just a quick demo)
Testing
Now when we visit our VPS IP we will get the traffic redirected through our VPS hosted server back to our backend web server:
Now port scan/http request from another public IP. You can also use a service such as shields up.
Summary
Here we have a simple setup for forwarding traffic from a VPS to a web server at another public facing IP. You could deploy many VPS forwarders and have these redirect traffic back to infrastructure. There are key opsec considerations here but hopefully this has given you an idea of the overall architecture and demo setup. You would want to look at using a defence in depth approach to secure the back end infrastructure and redirectors.









