Leadership
Leadership
Measuring Cyber Defence Success
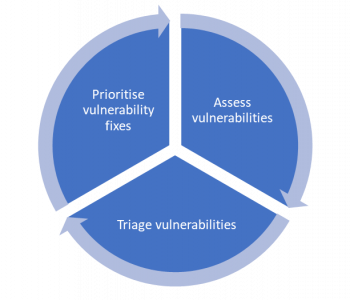
What does “good” cyber security look like? Sure, we can run a maturity assessment and see what good indicators are and we can create a baseline of our current state to establish where we are and what gaps we have (honestly in real terms this isn’t something to consider you should be doing this!) but how do we measure success in cyber security? Is every success an invisible outcome? Because one question that often comes to mind here is, just because we don’t see something, does that mean everything is ok? In the fast-paced world of cyber security, measuring success isn’t as easy as you would think. I’ll give an example of this, let’s say we don’t monitor, we get breached, but the threat actor just performs crypto mining (let’s say this is on premises) and we never really notice in the grand scheme of the world that our energy consumption costs have increased, if we didn’t know this had occurred, we might think our security is good. Read more “Measuring Cyber Defence Success”