 Education
Education
The loss of availability Ransomware causes is enough to make your day/week/s bad, the loss of data, bad month/quarter or longer.
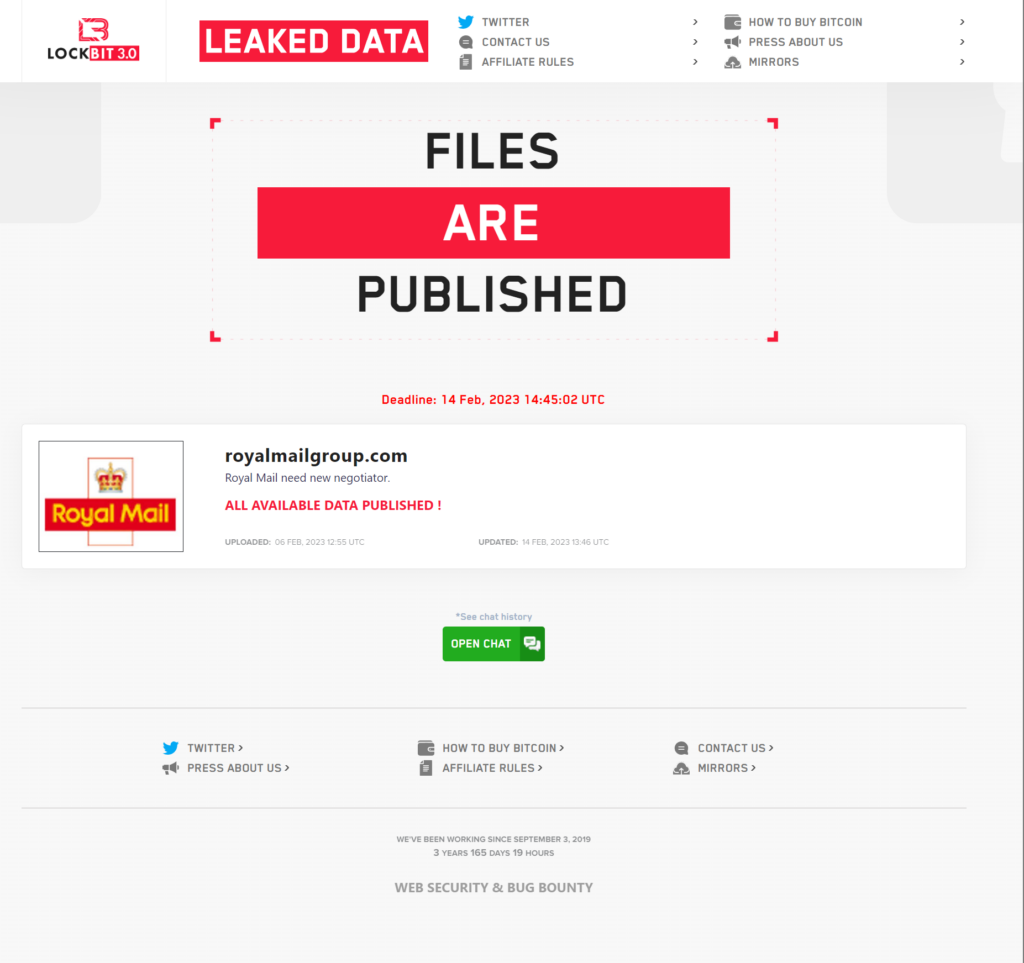
Lockbit posted “Royal Mail need new negotiator.” Followed by “ALL AVAILABLE DATA PUBLISHED !”
What we actually found is that they published the chat history:
Now what exactly was in this chat?
Now I’ve slightly redacted some URLs here but here is what Lockbit published (it’s literally on their website, so It’s not like there’s any secret to seeing this if you visit the Lockbit Onion site). Why publish this? Lots of people will not (and hopefully never) need to see what occurs during a negotiation with a ransomware group (criminals) so this should be educational and help people see behind what is probably a curtain to many.
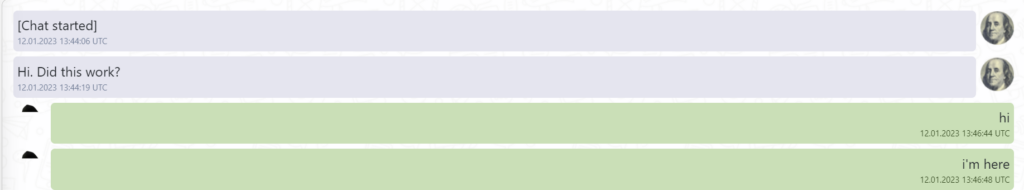
So here it is:
[Chat started]
12.01.2023 13:44:06 UTC
Hi. Did this work?
12.01.2023 13:44:19 UTC
hi
12.01.2023 13:46:44 UTC
i'm here
12.01.2023 13:46:48 UTC
http://[REDACTED]
12.01.2023 13:47:01 UTC
tree stolen data
12.01.2023 13:47:07 UTC
password @f[REDACTED]
12.01.2023 13:47:34 UTC
Now I am worried about the other link with data in the other chat. Is that link gone now? so no one sees it
12.01.2023 13:47:40 UTC
If you have already downloaded it, it is no longer available
12.01.2023 13:48:54 UTC
Thank you.
12.01.2023 13:49:09 UTC
Is this showing all the data you have taken from us?
12.01.2023 13:49:28 UTC
the link is not available, did you download the tree or download it again?
12.01.2023 13:49:41 UTC
Yes, all stolen data
12.01.2023 13:50:05 UTC
I did open it and download a file from it. Is that the data?
12.01.2023 13:50:15 UTC
there was a tree of data stolen from us at the link. you can select some files, we will send them to you
12.01.2023 13:51:04 UTC
I will open the file and show it to my management
12.01.2023 13:52:12 UTC
Yes, don't delay. time is not playing in your favor. so far we have not reported the attack on our blog
12.01.2023 13:53:54 UTC
to whom am I speaking?
12.01.2023 13:54:10 UTC
I work in our IT. Our senior management have asked me to contact you as it said in your note
12.01.2023 13:55:54 UTC
ok
12.01.2023 14:14:34 UTC
what does management say?
12.01.2023 19:44:46 UTC
Hi. I gave them the file. I am still waiting for them to come back to me.
13.01.2023 15:31:42 UTC
ok. hurry up
13.01.2023 17:32:45 UTC
We shall return to speak on Monday following the weekend and lengthy discussions with our internal stakeholders.
13.01.2023 20:00:02 UTC
Try to spend them productively, and please us. our patience is not infinite
13.01.2023 20:56:51 UTC
what can we expect by monday?
13.01.2023 20:58:19 UTC
We will let you know
13.01.2023 20:58:47 UTC
ok
13.01.2023 20:59:18 UTC
Hello. We waited the time you asked for. Now it's time to pay.
16.01.2023 21:47:26 UTC
Apologies for the delay as this is a lot for us to deal with. We shall get back to you tomorrow with some file names from your large list to request to see.
17.01.2023 19:12:33 UTC
File: [requested_files.txt]
18.01.2023 17:16:04 UTC
These are the files we would like to see that you have
18.01.2023 17:16:27 UTC
http://[REDACTED]
18.01.2023 19:16:19 UTC
pass pMjd07L82^VYVexJyF6etQZ31
18.01.2023 19:16:34 UTC
Hello, it's time to pay.
20.01.2023 11:29:08 UTC
What do we need to test your decryption ability with our files?
20.01.2023 14:54:24 UTC
each machine has its own ID. In order to decrypt the file you need to take the file from one PC, and go to the chat with the ID of this PC. then the test decrypt will be successful
20.01.2023 19:30:05 UTC
Okay, we'll see what we can do to identify the ID from each. Will come back to you.
20.01.2023 20:07:52 UTC
Also you can send me 5-10 files, I will decrypt it for you
20.01.2023 21:28:19 UTC
Use this sites File Share: [REDACTED]
20.01.2023 21:28:36 UTC
Think I did this right. Here's some files: http://[REDACTED]
21.01.2023 04:00:32 UTC
I also have a 6 GB file that is very important. It's associated with medical devices that can't yet be shipped out because this file is locked. Please please if you can unlock this too it will help save lives. I don't know how to send it over
21.01.2023 04:03:07 UTC
File: [1.png]
21.01.2023 13:12:02 UTC
File: [2.png]
21.01.2023 13:12:08 UTC
File: [3.png]
21.01.2023 13:12:15 UTC
File: [smh_installer.log.7z]
21.01.2023 13:12:49 UTC
File: [WindowsUpdate.log.7z]
21.01.2023 13:12:58 UTC
You gave me valuable files that can help restore your systems without paying for a decryptor, so I only gave back some of your files, and screenshots of the valuable files.
21.01.2023 13:22:32 UTC
About 6 gigabytes of data that will supposedly save someone's life, is it one file weighing 6 gigabytes, or is it many files weighing 6 gigabytes in total? Something tells me that you are bluffing and you are doing system recovery and want to get free decryption of critical files needed for recovery. Tell me in detail what the medical equipment is and what the 6 gigabyte files are.
21.01.2023 13:24:40 UTC
There are 2 files that are a combined 6 gigabytes when compressed. You know how much of our data is encrypted and when you see the files, you will understand that they will not allow us to recover. We are only pressing this because of the medical concern and we do not believe that your intent is to hurt anyone.
21.01.2023 16:28:17 UTC
What are these files? What is their function? What medical equipment are these files for? And what does the postal service have to do with medical software? Where is the logic?
21.01.2023 20:35:45 UTC
We are not just a postal service. We handle both letters and parcels, where roughly 60% of our business is parcels - international export of global medical supplies, contribute to a significant element of that! These supplies include vital replacement equipment parts, COVID-19 test kits, prescription drugs etc. The files that we have provided should allow us to resume shipping some of this equipment, not only here in the UK, but globally as well. Our transportation of this medical equipment does play a vital role in ensuring that people in need are being helped by these products. Given that the files are renamed, we are making our best assumption that this is the right dataset, and we would greatly appreciate the assistance.
22.01.2023 18:15:53 UTC
If you pretend that you do not believe that the decryptor really works, you can send me 10-20 other less important files, e.g. not related to virtualization systems and not containing RAM dumps, you can send me personal documents, photos, and many other things that do not help you without paying for my postpaid pentest services. If you were really worried about medical equipment, just pay for my work and get a decryptor within 5 minutes. You are making multi-billion dollar profits from your business and don't want to part with the money, don't you think that's odd? It's your greed that makes the people who are waiting for their packages suffer.
22.01.2023 18:39:32 UTC
We are not pretending anything and apologise if it appears that way. It is just that my management have heard that your decryptor might not work on large files, that is why they asked and wanted to see if it did. I am trying to convince them to work with you here, they are just asking for more proof of what we will get from you. As you probably know, we are already a loss making company, so we are not gaining anything from dragging this out. There are several articles on Google about our financial situation and how bad it is currently.
24.01.2023 12:51:35 UTC
You can send me other large files, I will decrypt for you those files that I think are not valuable, that way you can be sure that the decryptor works on large files. Your financial situation is fine, you have a multi-billion dollar turnover, and a huge profit, the sooner you pay, the sooner this whole nightmare will be over for you. If you continue to stretch time I will be forced to publish your information on the blog with an offer to change negotiators, thank you for your understanding.
24.01.2023 13:47:58 UTC
We are collecting some larger files that are not valuable to provide you. It's important for us to understand these can be decrypted of course so we appreciate you providing that opportunity to us. Ahead of this, we haven't even heard from you what it is that you want.
25.01.2023 17:27:01 UTC
I'm waiting for the next batch of files to be decrypted. We want as 0.5% of your revenue.
25.01.2023 17:52:34 UTC
And how much is that?
25.01.2023 17:55:27 UTC
How much your revenue?
25.01.2023 17:55:48 UTC
All we have had is losses. Here, you can read about it yourself. https://www.thetimes.co.uk/article/royal-mail-losses-rise-to-450m-ls8bjvv5b https://www.theguardian.com/business/2022/oct/14/royal-mail-to-cut-up-to-10000-roles-blaming-strikes-and-lower-parcel-volumes
25.01.2023 17:57:54 UTC
We understand you very well, we are all suffering from the global crisis and our income has fallen as much as yours, anyway you are hundreds of times richer than us. 0.5% of annual global turnover is much less than a 4% fine from your government.
25.01.2023 18:05:40 UTC
Just name the amount already so we can let the leadership know.
25.01.2023 18:12:52 UTC
$80 million is 0.5% of your revenue, $640 million is 4% of your revenue. We are asking 8 times less than your state. In addition to this price you get a decrypt of your data.
25.01.2023 18:17:10 UTC
Do you really think the government doesn't already know about this? Even if they were to fine us, paying you or not does not change this.
25.01.2023 18:28:24 UTC
We'll get you the files and we can continue these talks later.
25.01.2023 18:32:06 UTC
As long as we haven't published any of your files, you can't be fined. If you can negotiate with us, the government will be left without your $640 million. It is much better for you to negotiate with us and continue your very successful business with a long history and impeccable reputation. I personally used the services of your company and was very satisfied. I wouldn't want you to suffer so much from the government.
25.01.2023 18:32:49 UTC
Talk to you later
25.01.2023 18:34:07 UTC
Ok
25.01.2023 18:34:15 UTC
How do I give you these large files? They are larger than your 2GB limit
26.01.2023 19:35:54 UTC
My internet does not allow me to download such huge files, my internet speed is 50 kilobytes per second, send me files up to 50-100 megabytes at most. At the same time I can offer you to do the following, I will create a build of the encryptor and give you together with the decryptor, you will encrypt any files on your virtual machine and this way you can check the successful decryption of files larger than 2 gigabytes.
26.01.2023 19:46:40 UTC
Okay, I guess we can try that. We just want to have confidence your decryption tool will work on these large files
26.01.2023 20:04:08 UTC
You don't have to worry, thousands of people have successfully decrypted their files for almost four years.
26.01.2023 20:11:35 UTC
I believe you, but we need to see it ourselves before we can consider this
26.01.2023 20:12:23 UTC
http://[REDACTED]
26.01.2023 20:17:33 UTC
Encrypt any of your computers or virtual machines, any amount or amount of information. Write to me via a note and I will give you a decryptor in a new chat in which you will write to me.
26.01.2023 20:18:51 UTC
To start the encryption, simply run the file as administrator.
26.01.2023 20:23:33 UTC
There is still some confusion over who we are, you are basing your revenue on what is a holding company and not Royal Mail Group. IDS (International Distribution Services) have several companies that exist under that umbrella who are independent to each other. We are Royal Mail International who is a separate entity, with an entirely independent Managing Director and Senior Official. Our Company’s revenue is in decline, as we have tried to explain to you previously and Royal Mail International is the Company that is affected by your penetration testing. Our current financial turnover is expected to be 800 million. Based on your calculation for payment (0.5% of total revenue) this equals 4 million dollars. If there is any negotiation at this percentage level the starting figure needs to represent what I have just described. I am trying to help our Senior Team understand this and I am grateful that you have offered to help them see that your decryptor can work to restore our services, by offering to decrypt some larger files. We will have to accept what we have for now and will see if this is good enough for them or not..
26.01.2023 21:58:06 UTC
You're bluffing, 800 million is your net profit per year, so 80 million is not that much money for you.
26.01.2023 23:41:08 UTC
What company are you looking at to get those numbers?
27.01.2023 13:45:18 UTC
https://en.wikipedia.org/wiki/Royal_Mail
27.01.2023 19:40:56 UTC
https://en.wikipedia.org/wiki/Simon_Thompson_(Royal_Mail)
27.01.2023 19:41:15 UTC
Royal Mail CEO confirms cyberattack downed UK postal service
27.01.2023 19:41:37 UTC
Trying to explain we are Royal Mail International, who is a separate entity, with an entirely independent Managing Director and Senior Official, and not "Royal Mail" as the overall entity. What you attacked is just a small portion and our revenue is not that of Royal Mail.
27.01.2023 23:20:22 UTC
Anyways, time for bed. The board has meetings this weekend and we will not have anything new to speak about until Monday while they make their decision.
27.01.2023 23:21:48 UTC
You are a very clever negotiator, I appreciate your experience in stalling and bamboozling, when you are trying to deceive you need to provide evidence for greater credibility, only a fool would believe in the honest word of a lawyer defending his client.
28.01.2023 01:33:39 UTC
Not here to deceive or bamboozle. Just being transparent about what we're doing. The board having meetings this weekend shows our seriousness. Please confirm you will wait for their decision on Monday
28.01.2023 13:06:43 UTC
Your seriousness can consist only in a desire to pay 80 million dollars, all other promises of meetings of your management, which allegedly will be held, this is just a tactical move, increasing the time of negotiations calculated that I will be nervous and agree to a smaller amount of money that you will offer. I am ready to wait until Monday, I am sure that your directors have more than 100 million dollars on their personal cryptocurrency wallet, so it will not take much time to finish this nightmare.
28.01.2023 16:25:17 UTC
As we informed you, we have a response from our board to provide you. Under no circumstances will we pay you the absurd amount of money you have demanded. We have repeatedly tried to explain to you we are not the large entity you have assumed we are, but rather a smaller subsidiary without the resources you think we have. But you continue to refuse to listen to us. This is an amount that could never be taken seriously by our board.
30.01.2023 21:12:55 UTC
If I did not want to make a deal with you, your data would have already been published and the decryptor deleted. I am not forcing you to prove anything, I just kindly asked, refusing to give me such simple information says that you do not intend to cooperate with me honestly and tell me the truth. We are not attacking critical infrastructure, your commercial mail company with dozens of similar competitors is not. If you believe the news that your management is releasing, your mail services are fully restored and you are functioning as you are, humanitarian and medical supplies will be successfully delivered by your competitors, you will just get a little less profit, because you are very greedy and don't want to pay for my services. I'm sure you could easily pay $80 million, your income allows you to do so. If you want a discount, then make a counter offer, we are here to have constructive negotiations, not for me to give you a discount after every bluff you make until you say I'm fine with getting a free decryptor and free removal of stolen information. Any specific offer you make will be considered. You have a chance to make me an adequate payment offer by consulting with your board of directors, whose salaries are in the hundreds of thousands of pounds, but that does not stop them from being very greedy and not making concrete proposals to save the reputation of your commercial company which has more reasonable competitors who have already paid us money and successfully continue to earn new excess profits billions of pounds. Good day gentlemen.
31.01.2023 23:55:53 UTC
I am still trying to work with you here. I am trying to get the board to find a solution with you, but they have two major concerns. You haven't showed us that you could handle the large files, and your starting point here is way too high. We have told you who we are, and our numbers wouldn't at all justify the demand you have put forward. I am doing what I can to drive things forward on my end, but your demand is simply too high for the board to consider. If you can give me a lower starting point, I think I may be able to get the board to work with you. I really want to find a solution here, please help me do that.
01.02.2023 21:41:07 UTC
I'm ready to help you, I want to make money just like you, you and I have the same motivation in the form of money, your task is to reduce the price as much as possible, my task is to get the maximum amount. I have shown you that I can handle large files, you can encrypt and decrypt any files you want, why haven't you done that until now? The price is based on a multi-billion dollar company's profits, it's not the case that a company making billions of dollars pays the same price as an ordinary company making tens of millions of dollars. The more profits a company makes, the higher the buyout price, that's the math, you and your board of directors should understand that. Out of respect for you, I'm willing to step up and give you a 12.5% discount.
01.02.2023 23:24:58 UTC
Thank you for this. I appreciate you coming forward like this. I will bring this to my management and get back to you.
02.02.2023 21:16:44 UTC
Ok.
03.02.2023 10:14:28 UTC
I just want to let you know, that I am still waiting for a reply. My manager told me, that he is waiting to hear back from the board. He has promised me I’ll get an answer on Monday. I will let you know as soon as I hear anything.
03.02.2023 20:54:50 UTC
Very long, the company from the UK paid on the second day after the attack because they care more about their business and reputation, strange that for you it is not so important, because you make a lot more money.
03.02.2023 21:01:26 UTC
Maybe you didn't ask them for such a large amount. That would probably make it easier to pay quickly. My manager hasn't gotten an update from the board yet, can I check back in with you Monday?
04.02.2023 13:26:31 UTC
Naturally, I asked them for a smaller amount, their revenue is 58 times less than yours, they earn money 58 times less than you, I always ask for a fair and adequate amount from each company, I do not ask for what the company can not pay. Why do you have such a long chain of middlemen? why can't you communicate directly with the director? I will wait until Monday, but I think it is time to end this case. The journalists are asking me why I haven't published your information while I ignore their questions, they really want to see your files.
04.02.2023 16:40:24 UTC
You need pay.
06.02.2023 11:17:00 UTC
http://lock[REDACTED]
06.02.2023 12:52:43 UTC
You have 50 hours for payment.
06.02.2023 12:52:56 UTC
I just want to let you know, that I am still waiting to hear back from my management. It is not a quick decision for them, and I can’t just tell the board to hurry up. To be honest with you I have heard that they might not want to pay you for this. In our perspective the files got leaked when you took them from our system, and paying you won’t undo that in any way. I will get back to you as soon as I have further news.
06.02.2023 22:20:26 UTC
I just want to let you know that the data is ready to be published and the decryptor is ready to be deleted. You have had plenty of time to make your decision, your time is up.
07.02.2023 03:42:02 UTC
Do you have any offer for me?
09.02.2023 12:41:40 UTCI’m sure lots of people will dissect this line by line, for me the incident shows that the best way to negotiate a ransomware attack is to PREVENT it occurring in the first place!
This ransomware event is probably far from over, Lockbit didn’t release any data yet…. maybe they don’t have anything sensitive?
Ransomware Negotiation Themes
This is just a quick summary of themes in this chat, this should not be considered advice or a playbook:
- Make Contact
- Request for proof of data theft
- Request full list of files/data
- Request for sample (specific samples where sensitive data would be)
- Request for proof of ability to decrypt
- Advise Low Skilled/Low Authority in org
- Advise constant requirement for comms to go up to senior management (delay)
- Advise constraints on money
- Advise the threat actors have bad intelligence and that the impacted assets are part of a different org/subsidiary etc.
- Push for discounts/price reduction in relation to revenue
- Advise that it is a “big decision” and is with the board
- Keep updating the threat actors with progress, even if this is to just say “we are waiting for a board response)
- Set expectations of likely decision-making times
Defense
Now if you are worried about ransomware then you should realize it’s not a game you can’t win! There is not magic that makes ransomware work, it’s misconfigurations, vulnerabilities and a lack of investment in securing your digital assets! These events are largely NOT sophisticated, they don’t tend to leverage a chain of zero days and they often work because of misconfiguration. So let’s head over the UK NCSC and see what guidance they have:
https://www.ncsc.gov.uk/guidance/mitigating-malware-and-ransomware-attacks
Also look at Cyber Essentials, it covers of big chunks of activity that will help support posture improvement, it doesn’t cover every ransomware defense capability but it’s a good starting point:
https://www.ncsc.gov.uk/cyberessentials/overview
I’ve also written some blogs before about defending against ransomware:
Also look at other NCSC offerings:
https://www.ncsc.gov.uk/section/active-cyber-defence/introduction
https://www.ncsc.gov.uk/information/exercise-in-a-box
https://www.ncsc.gov.uk/information/early-warning-service
https://www.ncsc.gov.uk/information/pdns
Remember, each network is unique, there are huge common patterns of vulnerability leveraged during ransomware events however the specific of your environment matter!
“Know yourself, know your enemy” – honestly with ransomware if you know yourself you can probably let the CTI, Marketing and Press take care of the “know you enemy part” largely. The baddies use the same techniques that penteters and red teamers (and sysadmins!) use!
You can prevent these events, it just requires deciding to do so, investing appropriately, and the enabling and supporting your staff/team/service providers to make your “NETWORK” (I mean all of it, devices, people, serves, applications, data, networks) posture strong! And don’t forget about monitoring! It doesn’t take a million queries in a SIEM to find common ransomware actions… but you need centralized logs to start with (in a format that is useful and searchable with alerting and visualisations)
Hopefully this post helps people see behind the curtain, WE CAN BEAT ransomware but it does require a whole of society, industry, academia, government and community approach! (and it requires international efforts!)
If you have made it this far, would you mind completing a really short survey for me? It’s to help me focus on subjects and content to help people








