Defense
Defense
Risk management is easy! Isn’t it?
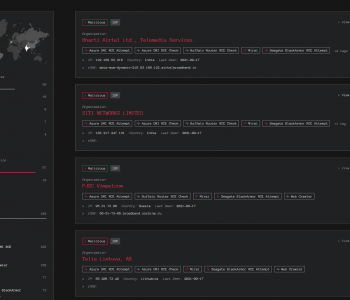
Information security theory and practises use a commonly understood and simple range of tools, methods, and practises to help organisations understand their risk portfolio and to enable them to make both strategic and tactical investment decisions….
Ok someone pinch me. this simply isn’t the reality I see on the ground. The theory is vast, complex and there are a multitude of good/best/insert phrase frameworks and tools that you can leverage to map, model, and communicate risks, vulnerabilities, controls, threats etc.
I’m not going to do a detailed analysis and comparison of different models here, but I am going to at least give people a view of some of the tools and frameworks that you can and may likely experience in the cyber security world. Read more “Risk management is easy! Isn’t it?”