Using CTFs for offensive and defensive training – Purple…
Pwning a legacy server on Hack the Box is good for a training exercise however what about if we want to think about how to use resrouces for red and blue. Looking at both sides of the coin when thinking about offense really should help people undesrand how to defend better. In the end of the day outside of a tiny tiny fraction of deployment types, you are going to need to be able to explain how to defend regardless of engagement type (vulnerability assessment, penetration test, purple team, red team etc.)
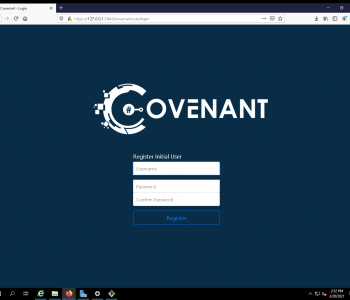
Getting access
I’m not going to talk through every step but here’s the commands you would need to run:
Read more “Using CTFs for offensive and defensive training – Purple Teaming”