Uncategorized
Uncategorized
Password audits, if you ask some security pros you will hear a million reasons why you would be insane to do them… ask me however and the answer is more nuanced. They are activities that must be handled with the upmost care, however…. they (in my experience) have been incredibly useful to help improve security postures and to enable organisations to understand risk! You are of course free to ignore what I think and live like an ostrich (or it really might not be suitable for your environment). I’m not going to talk about how to do a password audit today, I’m also not going to advise in this post on sourcing strategy (you may want to do in house or you might want to outsource, after all, you normally put all your hashes in someone else’s computer when you use cloud right!?), anyway enough rambling, year ago the NCSC UK did some password auditing research (it was good work – Spray you, spray me: defending against password spraying… – NCSC.GOV.UK) and now the DOI have also done similar, check out the report In the link below:
For those who want a TLDR (in the words of Dan) here’s a summary
Findings
- The Department’s Ineffective Password Complexity Requirements Allowed Easy-To-Crack Passwords
- The Department’s Password Complexity Requirements Implicitly Allowed Hundreds of Unrelated Accounts to Use the Same Passwords
- The Department Did Not Timely Disable Inactive Accounts or Enforce Password Age Limits
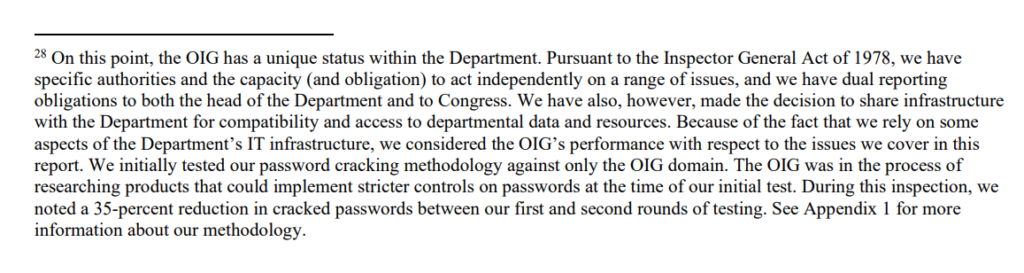
Footnote
This is worth reading as well…
Recommendations (Paraphrased)
- Prioritise MFA
- Have a mechanism to track MFA deployment status.
- Revise password complexity based on NIST SP800-63
- Implement controls to limit/restrict use of commonly weak/compromised passwords.
- Ensure controls are enforced, monitored etc.
- Prohibit sharing of passwords/passphrases between accounts.
- Make temporary passwords unique and complex.
- Ensure accountability for compliance of policies, ensure accounts are monitored, managed and where not required disabled in a timely manner.
My Summary
Passwords, lots talks about passwordless but it’s usually not a reality for MOST orgs or people, there’s still tons of barriers to entry (they are slowly being eroded) so it’s likely you will need to have a strategy for ensuring you have strong authentication and controls! That might include regular password audits, it might not. Either way, passwords are a part of life! A dodgy one and a weak posture and you might be dealing with an act of Ransom (ransomware etc.) or a business email compromise (BEC) so it’s a bloody good idea to know what your risks are.
Also controls – if you use Azure AD think about:
- Conditional Access
- MFA
- Risky Sign Ins
- Monitoring with MDE or Sentinel
- Defender for Identity/Cloud also has SMART LOCKOUTS etc.
Go read the vendor docs from your cloud provider etc.
Also for lulz:
My WordPress creds are as follows:
pwndefendwordpress
Password123!
Enjoy!
Oh and if you wanted to know how to use L0phtcrack I wrote a quick guide, or so a friend told me, I had forgotten 😀 Password Auditing with L0phtcrack 7 – A quick intro – PwnDefend (now remember this is risky, and you need to not piss about so take MASSIVE LOADS OF PRECAUSTIONS)