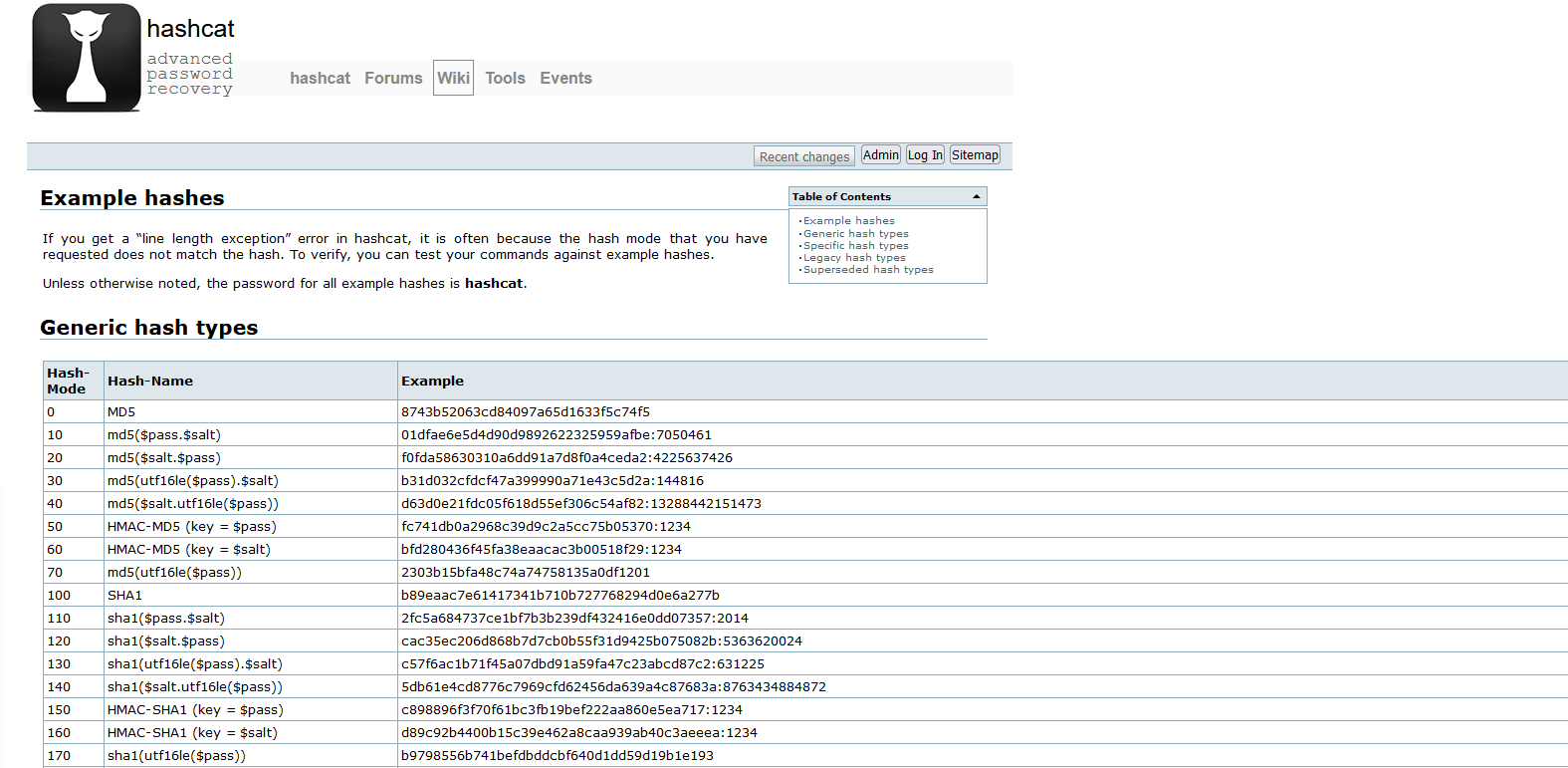
How to Crack NTHASH (commonly referred to as NTLM)…
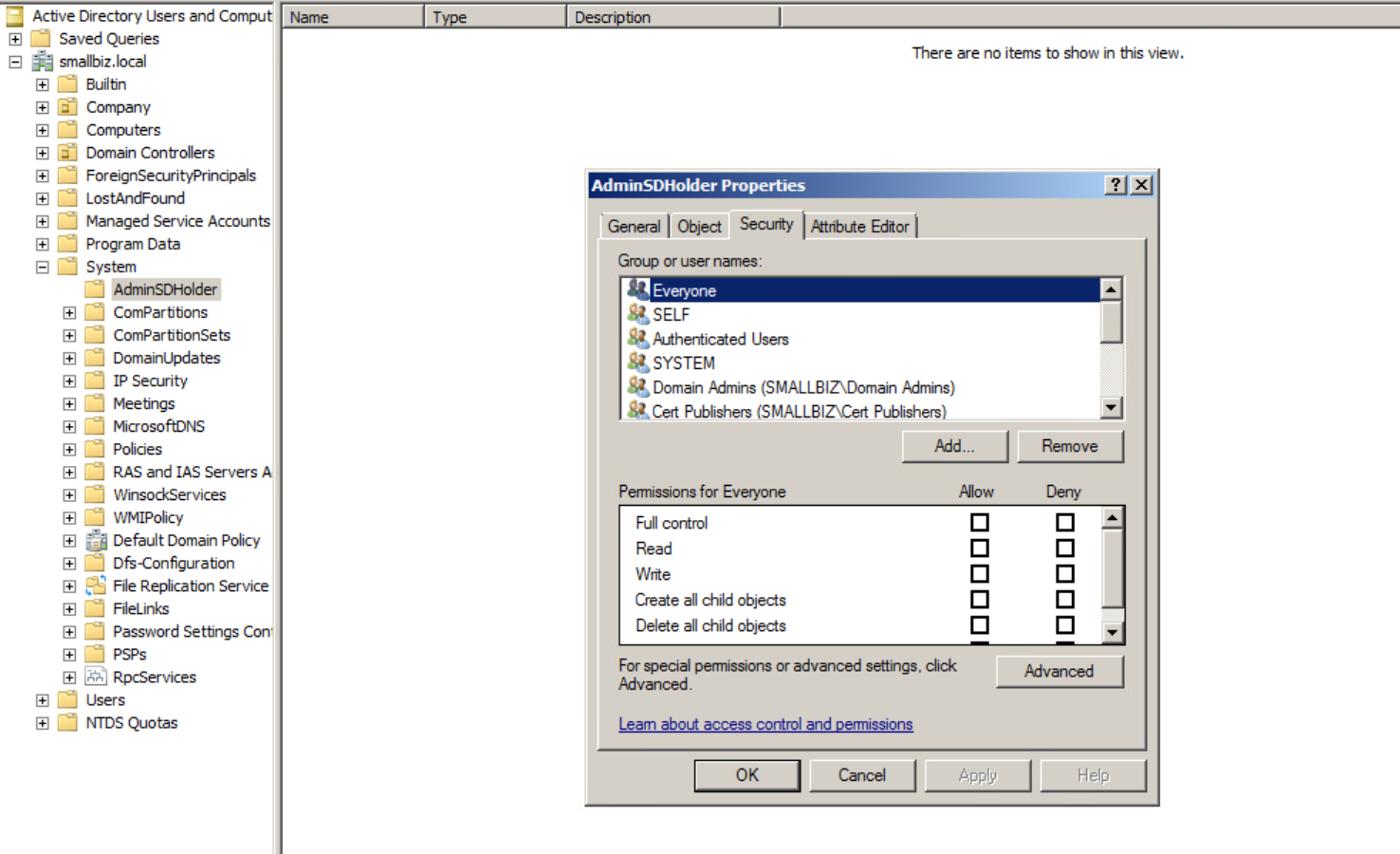
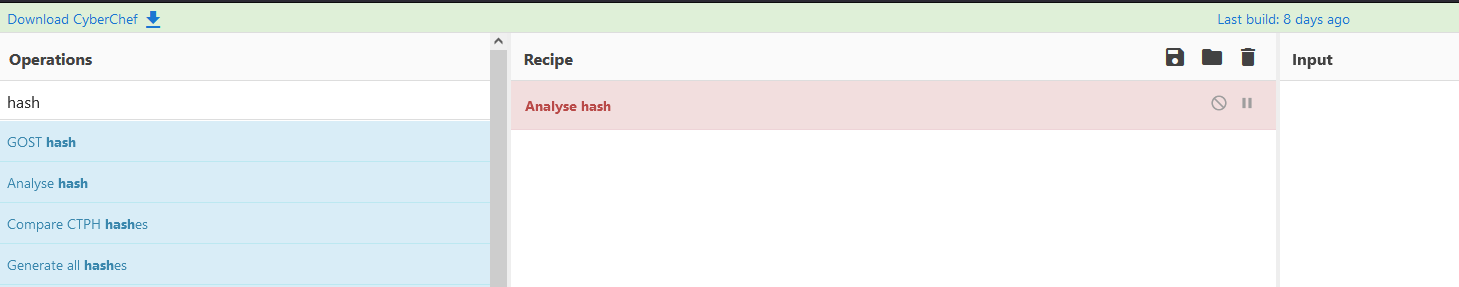
Ok imagine this, you have got access to a file server and behold you find an unsecured, unencrypted backup of a domain controller (this isn’t made up I find these in networks sometimes!) and you yoink the NTDS.dit (or maybe it’s just a workstation SAM/SYSTEM file), you extract the hashes but now what, you need to crack those bad boys!
Check out the MS docs on how NT or LM Hashes are computed(hashed)! – (thanks @ANeilan for spotting my mistake!)
[MS-SAMR]: Encrypting an NT or LM Hash | Microsoft Docs
Read more “How to Crack NTHASH (commonly referred to as NTLM) password hashes?”