CTF
CTF
How to Identify Hashes
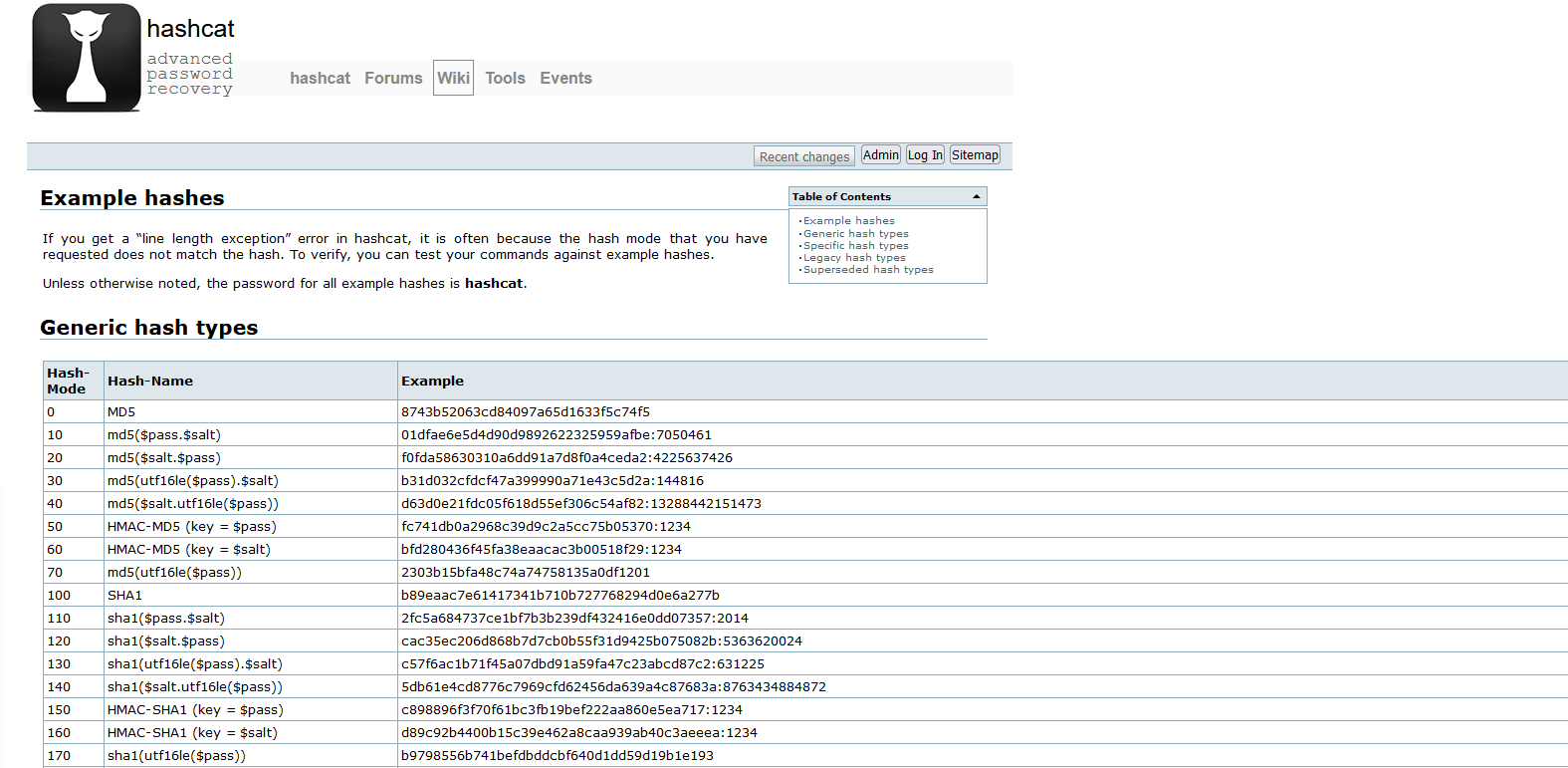
Some hashes are obvious but even then, it’s a good job to check. There are a few ways to check a hash outside of manual validation.
Using the Hashcat example list:
https://hashcat.net/wiki/doku.php?id=example_hashes
Using hash-identifier:
https://github.com/blackploit/hash-identifier
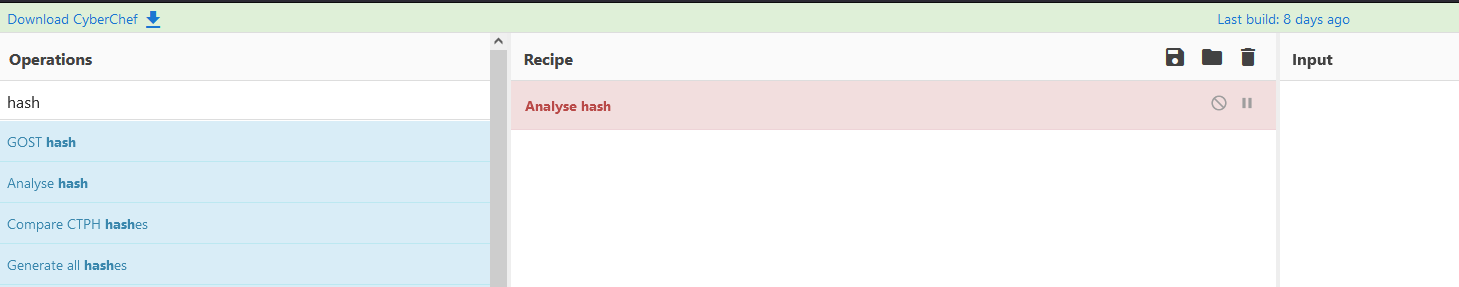
Using cyberchef Analyse hash:
https://gchq.github.io/CyberChef/#recipe=Analyse_hash()
Using hash-id:
https://github.com/psypanda/hashID
Using HashTag:
https://github.com/SmeegeSec/HashTag
As you can see there are range of tools available to you, and remember if you want to keep the hashes to yourself you can download Cyberchef and run it locally!